Blog
Featured Story![2025 Gartner Magic Quadrant for Cloud DBMS]()

News
November 21, 2025/5 min read
Databricks Named a Leader in 2025 Gartner® Magic Quadrant™ for Cloud Database Management Systems
What's new![A Year of Interoperability: How Enterprises Are Scaling Governance with Unity Catalog]()

Product
November 26, 2025/5 min read
A Year of Interoperability: How Enterprises Are Scaling Governance with Unity Catalog
Recent posts

Energy
December 4, 2025/4 min read
BP’s Geospatial AI Engine: Transforming Safety and Operations with Databricks

Data Leader
December 4, 2025/2 min read
Building the AI-Ready Enterprise: Leaders Share Real-World AI Solutions and Practices

Announcements
December 2, 2025/6 min read
Completing the Lakehouse Vision: Open Storage, Open Access, Unified Governance

Healthcare & Life Sciences
December 1, 2025/3 min read
Databricks and NVIDIA: Powering the Next Generation of Industry AI
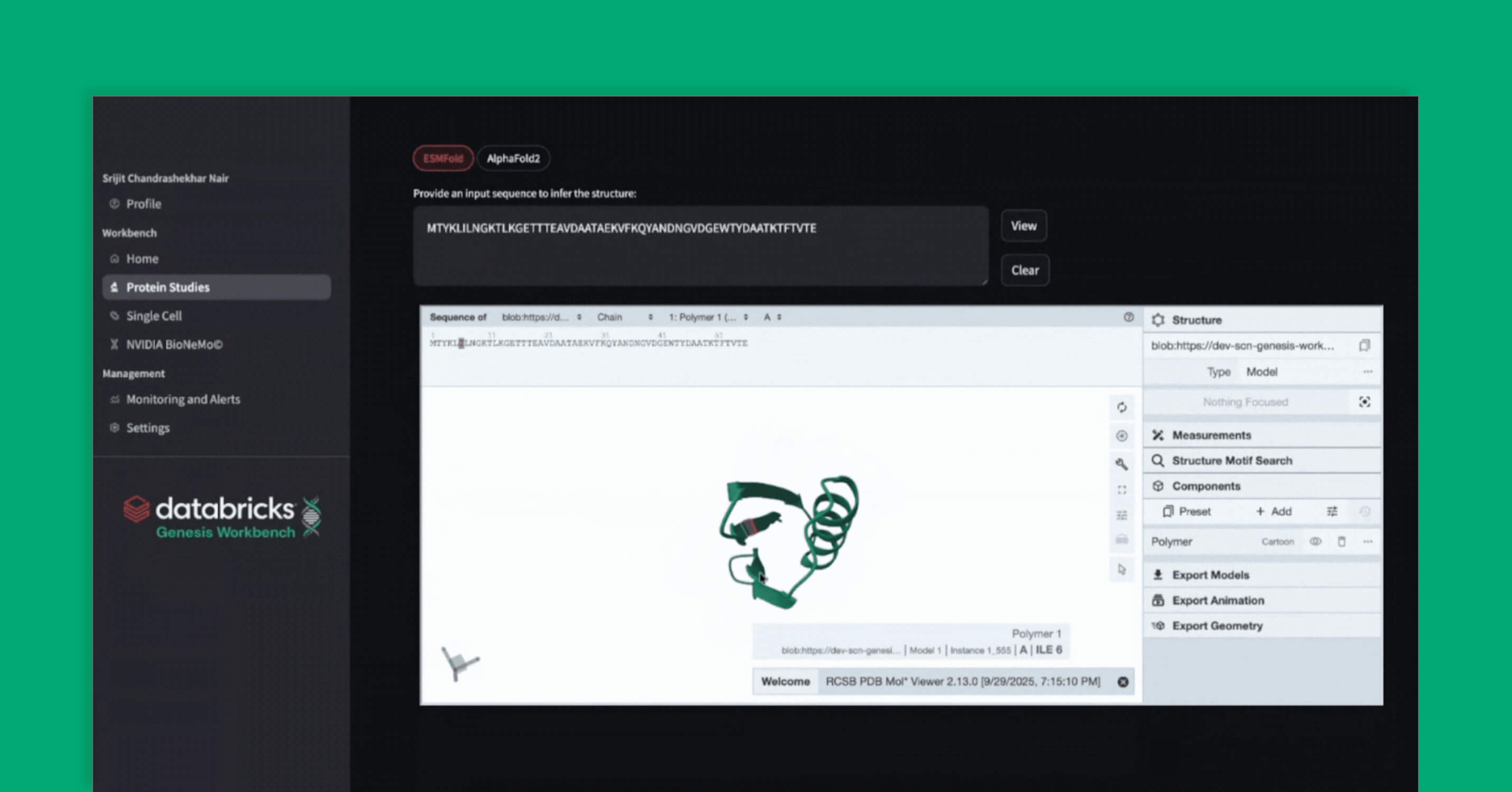
Mosaic Research
December 1, 2025/14 min read
Genesis Workbench: A Blueprint for Life Sciences Applications on Databricks

Data Engineering
December 1, 2025/11 min read
From Events to Insights: Complex State Processing with Schema Evolution in transformWithState
Partners
November 26, 2025/4 min read
From Blind Spots to Real-Time Intelligence: How Location Data from O2 Motion is Transforming Business Decision-Making

Product
November 26, 2025/5 min read
A Year of Interoperability: How Enterprises Are Scaling Governance with Unity Catalog

Company
November 24, 2025/6 min read
Building the Future of AI Agents and Intelligence Apps: Celebrating 4 years of Databricks Seattle R&D

News
November 21, 2025/5 min read
Databricks Named a Leader in 2025 Gartner® Magic Quadrant™ for Cloud Database Management Systems

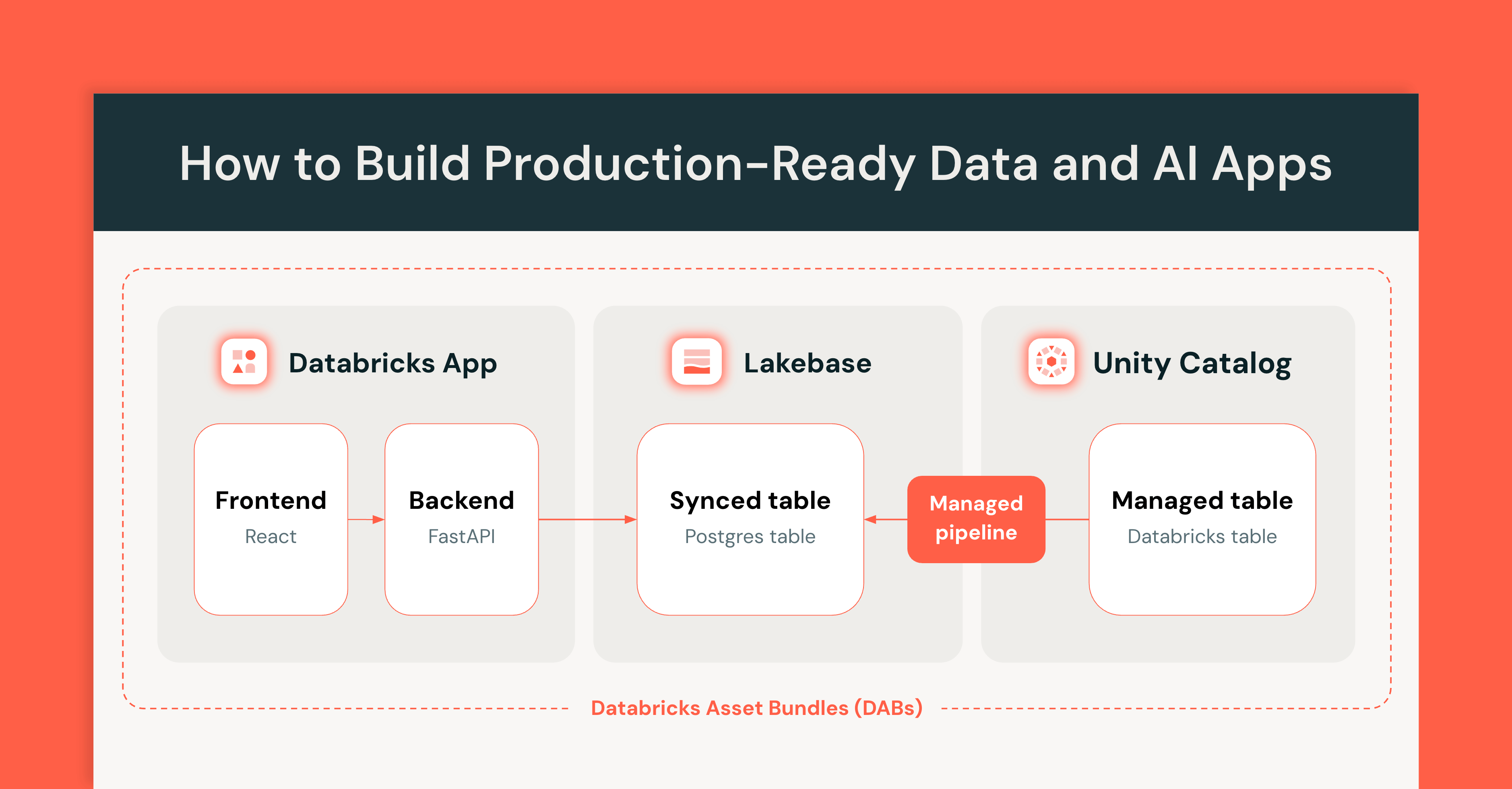
Platform
November 21, 2025/4 min read
Redefining the Data Warehouse for the AI Era with Azure Databricks
Product
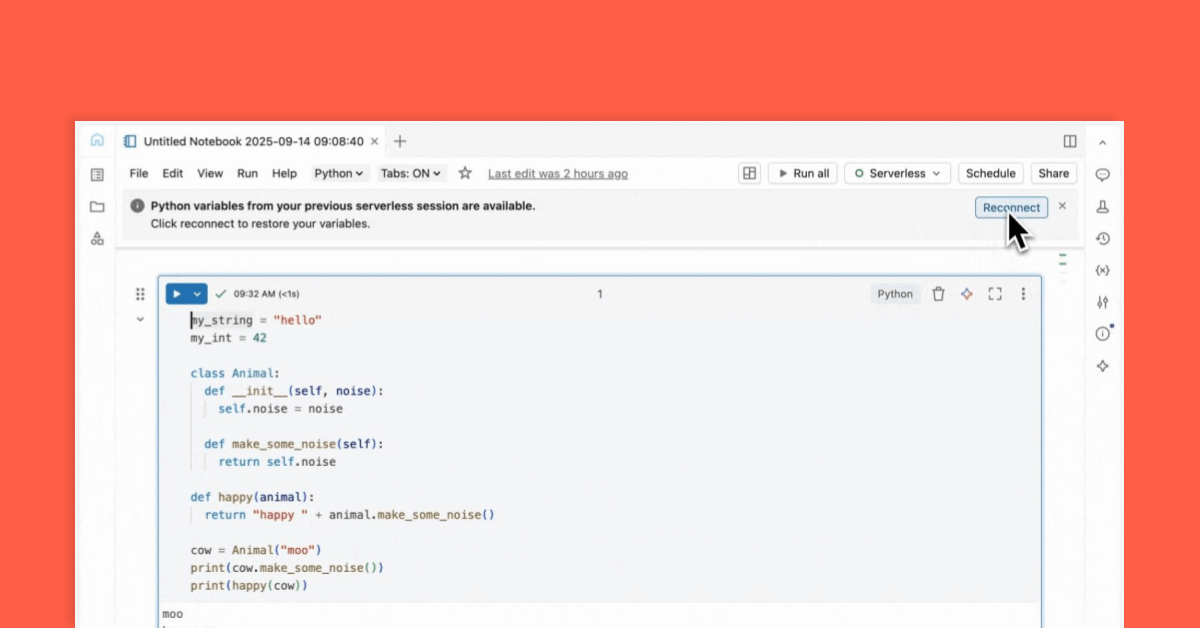
November 19, 2025/11 min read
How to Build Production-Ready Data and AI Apps with Databricks Apps and Lakebase
Data Intelligence for All
Never miss a Databricks post
Subscribe to our blog and get the latest posts delivered to your inbox